Sender Policy Framework
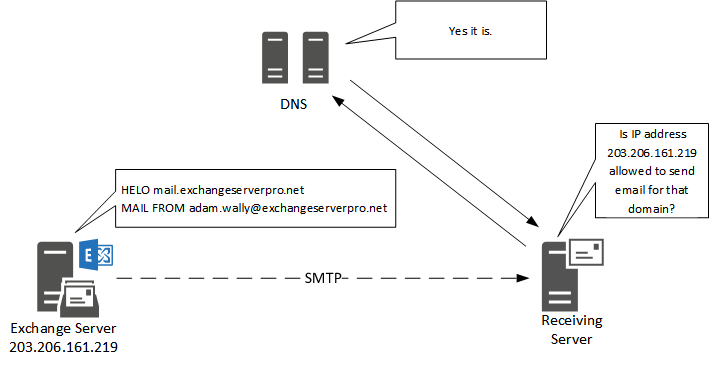
Sender Policy Framework (SPF) is an email authentication method designed to detect forging sender addresses during the delivery of the email. SPF alone, though, is limited only to detect a forged sender claimed in the envelope of the email which is used when the mail gets bounced. Only in combination with DMARC can it be used to detect the forging of the visible sender in emails (email spoofing), a technique often used in phishing and email spam.
SPF allows the receiving mail server to check during mail delivery that a mail claiming to come from a specific domain is submitted by an IP address authorized by that domain’s administrators. The list of authorized sending hosts and IP addresses for a domain is published in the DNS records for that domain.
If you want to verify if your email domain has SPF correctly implemented, you can use online tools like MX Toolbox to verify this.
https://mxtoolbox.com/spf.aspx
References:
https://en.wikipedia.org/wiki/Sender_Policy_Framework
DomainKeys Identified Mail
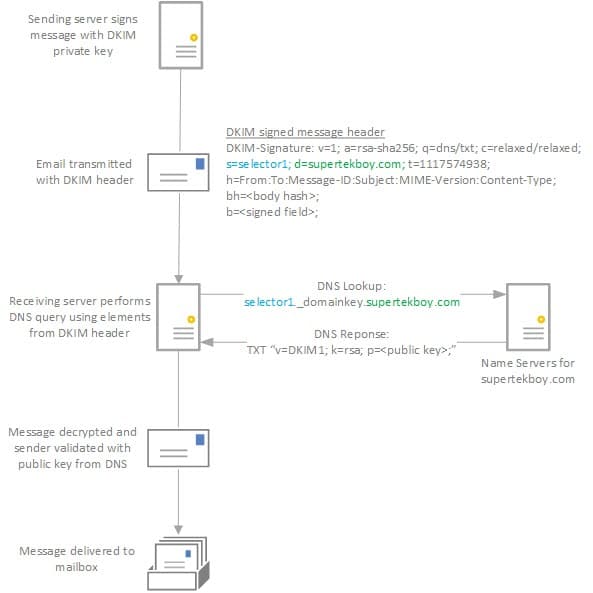
DomainKeys Identified Mail (DKIM) is an email authentication method designed to detect forged sender addresses in emails (email spoofing), a technique often used in phishing and email spam.
DKIM allows the receiver to check that an email claimed to have come from a specific domain was indeed authorized by the owner of that domain. It achieves this by affixing a digital signature, linked to a domain name, to each outgoing email message. The recipient system can verify this by looking up the sender’s public key published in the DNS. A valid signature also guarantees that some parts of the email (possibly including attachments) have not been modified since the signature was affixed. Usually, DKIM signatures are not visible to end-users, and are affixed or verified by the infrastructure rather than the message’s authors and recipients.
References:
https://nl.wikipedia.org/wiki/DomainKeys_Identified_Mail
https://supertekboy.com/2016/06/27/enable-dkim-signing-office-365/
Howto – Set up DKIM Signing on postfix
$ apt-get install openssl $ openssl genrsa -out myemaildomain.com.private.key.pem 1024 -outform PEM $ openssl rsa -in myemaildomain .com.private.key.pem -out myemaildomain .com.public.key.pem -pubout -outform PEM # Create a TXT dns record smtprelay._domainkey. myemaildomain .com with the value "k=rsa; p=your public key" $ apt-get install opendkim opendkim-tools $ adduser postfix opendkim $ chown opendkim:opendkim /etc/postfix/ myemaildomain .com.private.key.pem $ chmod 600 /etc/postfix/ myemaildomain .com.private.key.pem
$ cat << EOF > /etc/opendkim.conf # This is a basic configuration that can easily be adapted to suit a standard # installation. For more advanced options, see opendkim.conf(5) and/or # /usr/share/doc/opendkim/examples/opendkim.conf.sample. # Log to syslog Syslog yes # Required to use local socket with MTAs that access the socket as a non- # privileged user (e.g. Postfix) UMask 002 # OpenDKIM user # Remember to add user postfix to group opendkim UserID opendkim # Map domains in From addresses to keys used to sign messages KeyTable /etc/opendkim/key.table SigningTable refile:/etc/opendkim/signing.table # Hosts to ignore when verifying signatures ExternalIgnoreList /etc/opendkim/trusted.hosts InternalHosts /etc/opendkim/trusted.hosts # Commonly-used options; the commented-out versions show the defaults. Canonicalization relaxed/simple Mode s SubDomains no #ADSPAction continue AutoRestart yes AutoRestartRate 10/1M Background yes DNSTimeout 5 SignatureAlgorithm rsa-sha256 # Always oversign From (sign using actual From and a null From to prevent # malicious signatures header fields (From and/or others) between the signer # and the verifier. From is oversigned by default in the Debian package # because it is often the identity key used by reputation systems and thus # somewhat security sensitive. OversignHeaders From EOF
$ chmod u=rw,go=r /etc/opendkim.conf $ mkdir /etc/opendkim $ mkdir /etc/opendkim/keys $ chown -R opendkim:opendkim /etc/opendkim $ chmod go-rw /etc/opendkim/keys
$ cat << EOF > /etc/opendkim/signing.table *@myemaildomain.com smtprelay EOF
$ cat << EOF > /etc/opendkim/key.table smtprelay myemaildomain.com:smtprelay:/etc/postfix/myemaildomain.com.private.key.pem EOF
$ cat << EOF > /etc/opendkim/trusted.hosts 127.0.0.1 ::1 localhost smtprelay smtprelay.myemaildomain.com myemaildomain.com 10.0.0.0/8 78.235.22.41/32 EOF
$ chown -R opendkim:opendkim /etc/opendkim $ chmod -R go-rw /etc/opendkim/keys $ systemctl restart opendkim $ systemctl status -l opendkim $ opendkim-testkey -d myemaildomain.com -s smtprelay $ mkdir /var/spool/postfix/opendkim $ chown opendkim:postfix /var/spool/postfix/opendkim $ sed -i 's/SOCKET="local:\/var\/run\/opendkim\/opendkim.sock"/SOCKET="local:\/var\/spool\/postfix\/opendkim\/opendkim.sock"/g' /etc/default/opendkim
$ cat << EOF >> /etc/postfix/main.cf # Milter configuration # OpenDKIM milter_default_action = accept # Postfix ≥ 2.6 milter_protocol = 6, Postfix ≤ 2.5 milter_protocol = 2 milter_protocol = 6 smtpd_milters = local:/opendkim/opendkim.sock non_smtpd_milters = local:/opendkim/opendkim.sock EOF
$ systemctl restart opendkim $ systemctl restart postfix
References:
https://www.linode.com/docs/email/postfix/configure-spf-and-dkim-in-postfix-on-debian-8/
DMARC (Domain-based Message Authentication, Reporting and Conformance)
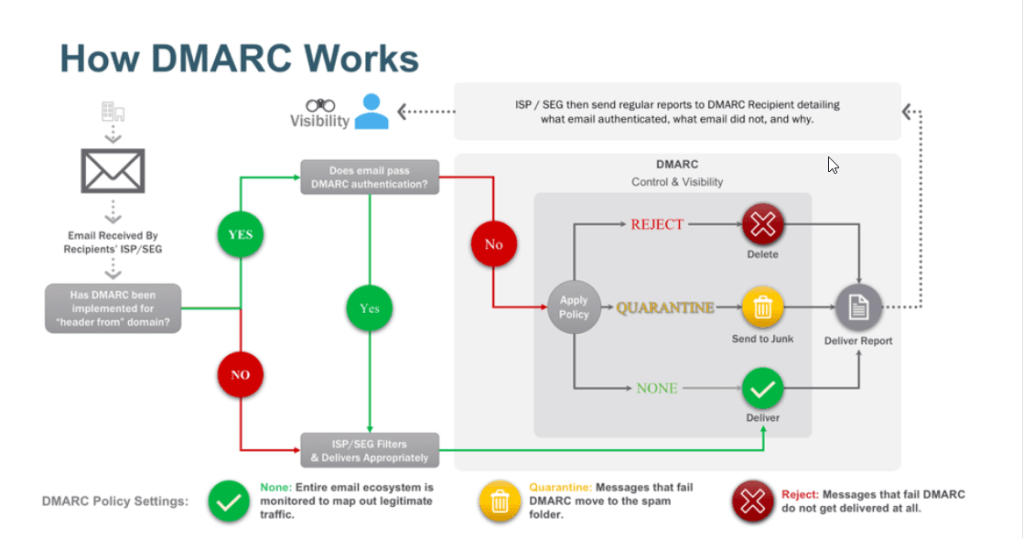
DMARC (Domain-based Message Authentication, Reporting and Conformance) is an email authentication protocol. It is designed to give email domain owners the ability to protect their domain from unauthorized use, commonly known as email spoofing. The purpose and primary outcome of implementing DMARC is to protect a domain from being used in business email compromise attacks, phishing emails, email scams and other cyber threat activities.
Once the DMARC DNS entry is published, any receiving email server can authenticate the incoming email based on the instructions published by the domain owner within the DNS entry. If the email passes the authentication it will be delivered and can be trusted. If the email fails the check, depending on the instructions held within the DMARC record the email could be delivered, quarantined or rejected.
DMARC extends two existing mechanisms, Sender Policy Framework (SPF) and DomainKeys Identified Mail (DKIM). It allows the administrative owner of a domain to publish a policy in their DNS records to specify which mechanism (DKIM, SPF or both) is employed when sending email from that domain; how to check the From: field presented to end users; how the receiver should deal with failures – and a reporting mechanism for actions performed under those policies.
References: