
If you love the NSA like I do and want to understand how they succeed in invading our privacy by breaking our encrypted communication, you need to digest a lot of theoretical resources about cryptography.
A lot of security protocols exist nowadays, SSLv3/TLSv1.2 and SSHv2 beïng the more known and used protocols.
Knowing the weaknesses of these protocols, and therefore beïng able to correctly implement these protocols in your networking infrastructure seems trivial nowadays if you want to avoid any man-in-the-middle listening in.

It seems evidently that an important factor for good security is the entropy of your random number data used to generate your secrets with.
Entropy is a measure for randomness, and provides a way to express the ‘quality of randomness’ of your starting number data for your secret.
If an attacker were to be able to predict the randomness of these numbers, he would subsequently be able to perform effective brute force techniques against the encrypted data, eventually revealing the contents of the encrypted data.
In our tutorial for today we will be visualising and testing random number data used as starting point for our cryptographical systems.
The Raspberry Pi has a TRNG (True Random Number Generator) built into it’s SOC.
We will check if the data produced by this TRNG is able to withstand a FIPS 140-2 test.
FIPS is the American Information Processing Standard.
First start off by downloading your copy of Raspbian Jesslie Lite from the Raspberry Foundation web site, write to SD card, boot it up, and log in with username pi and raspberry as password.
The release date of the Raspbian Jessie lite image used for this tutorial was 18/03/2016.
Note that for this installation a Raspberry Pi model B was used.
Update your Raspberry Pi
sudo apt-get update
sudo apt-get -y dist-upgrade
sudo rpi-update
To enable the True Random Number Generator on the Raspberry Pi a kernel module needs to be loaded:
bcm2708_rng or bcm2835_rng
The first one is from an older revision kernel, which is now obsolete I believe.
When performing an lsmod on the Raspbian Jessie Lite image we can see that the kernel module for the True Random Number Generator is already loaded.

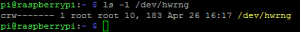
You can also verify it’s presence by checking if the /dev/hwrng entry exists.
If you notice that you don’t have this device available on your device, you can always load the kernel modules for it, either manually or at boot time.
modprobe bcm2835_rng # will load the kernel module on request
echo bcm2835_rng | sudo tee -a /etc/modules # add it to our modules file to load at boot-time
You can check it’s output by dumping a few raw blocks of it to stdout.
sudo dd bs=1024 count=2 if=/dev/hwrng of=-
A few blocks of random binary data should now be displayed.
Random data, when visualised, looks like static, or so-called snow, which you could see on an old television so many years ago. It’s truely random data visualised because of the absense of any predetermined signalling for visualisation.
On linux, we can visualise random data with the netpbm toolkit.
This toolkit can be installed with:
sudo apt-get install -y netpbm
Creating a visual image from the data can be accomplished by reading data bytes from the TRNG, converting these bytes into a portable pixmap, which is subsequently converted to a .png (image) file.
In below example, we read 1024 * 1024 = 1048576 bytes to convert it to an image
sudo dd bs=1b count=1048576 if=/dev/hwrng | rawtoppm -rgb 1024 1024 | pnmtopng > my-random-image-data.png
When viewing the image, we can see that it looks like static on our old television.

To test our random data for FIPS compliance we will need to install rng-tools:
sudo apt-get install rng-tools
rng-tools contains rngtest, a tool to test our random data against fips compliance.
It performs a series of statistical tests to determine if the entropy of our data matches up against FIPS regulations.
sudo cat /dev/hwrng | rngtest -c 1000
rngtest 2-unofficial-mt.14
Copyright (c) 2004 by Henrique de Moraes Holschuh
This is free software; see the source for copying conditions. There is NO warranty; not even for MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE.
rngtest: starting FIPS tests…
rngtest: bits received from input: 20000032
rngtest: FIPS 140-2 successes: 998
rngtest: FIPS 140-2 failures: 2
rngtest: FIPS 140-2(2001-10-10) Monobit: 0
rngtest: FIPS 140-2(2001-10-10) Poker: 0
rngtest: FIPS 140-2(2001-10-10) Runs: 1
rngtest: FIPS 140-2(2001-10-10) Long run: 1
rngtest: FIPS 140-2(2001-10-10) Continuous run: 0
rngtest: input channel speed: (min=17.254; avg=906.875; max=1502403.846)Kibits/s
rngtest: FIPS tests speed: (min=839.909; avg=4210.622; max=6403.689)Kibits/s
rngtest: Program run time: 27489439 microseconds
A few failures seems normal on these statistical tests, in our example case 0,2% of failures are noted against our data.
It gives you a fair idea how safe the entropy of your data is for usage in cryptographical systems.